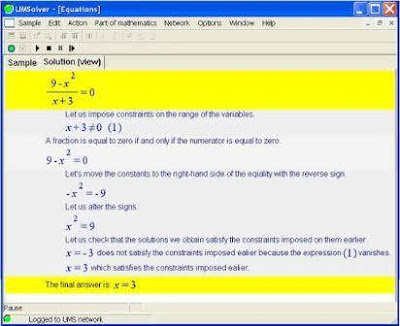
The Ultimate Math Solver! UMS - the indispensable student toolkit. UMS is a software package which, until now, students could only dream of. UMS solves any given problem, either one taken from a textbook or just invented on the spot. Moreover, UMS explains each step of the solution to the problem.
In general, there are a great many reasons why a student may have difficulty in assimilating a given mathematics lesson well. UMS deals with each of these difficulties, completely reconstituting the style of problem solving as taught in school. UMS produces the solution step by step on the computer monitor, accompanying the solving process with a professional teacher voice in your language of choice
And, UMS is being continuously developed and renewed. New versions with new features are regularly launched. In the foreseeable future UMS will include all the algebra and analysis of secondary school, and beginning university level courses as well.
Download:
http://rapidshare.com/files/33955556/Math.Solver.v5.0.1.3.rar
Pax Stand for Goddess of peace, So here m i Paras to Share My Knowledge(Links, hacks, Tricks) freely N Peacefully. Free full softwares, tricks , hacking material, everything u need!!!!!
Monday, May 5, 2008
The Ultimate Math Solver 5.0.1.3
Wireless Hacking Live-CD (FBI version)
{Must Have}
Hack a WLAN / Wireless Access Point
AND MORE, IT GOT EVERY PROGRAM THAT THE FBI WOULD USE!


Download:
Password:
Hack a WLAN / Wireless Access Point
AND MORE, IT GOT EVERY PROGRAM THAT THE FBI WOULD USE!
| Quote: |
This version is for all systems except systems with the Intel B/G wireless cards (IPW2200). - Live CD with all the tools you need to hack a WLAN / wireless Access point - Linux Live-CD - OS runs from CD - 635 mb - .iso - also used by the FBI … WEP Hacking - The Next Generation WEP is an encryption scheme, based on the RC-4 cipher, that is available on all 802.11a, b and g wireless products. WEP uses a set of bits called a key to scramble information in the data frames as it leaves the access point or client adapter and the scrambled message is then decrypted by the receiver. Both sides must have the same WEP key, which is usually a total of 64 or 128 bits long. A semi-random 24 bit number called an Initialization Vector (IV), is part of the key, so a 64 bit WEP key actually contains only 40 bits of “strong” encryption while a 128 bit key has 104. The IV is placed in encrypted frame’s header, and is transmitted in plain text. Traditionally, crac*ing WEP keys has been a slow and boring process. An attacker would have to capture hundreds of thousands or millions of packets—a process that could take hours or even days, depending on the volume of traffic passing over the wireless network. After enough packets were captured, a WEP crac*ing program such as Aircrac* would be used to find the WEP key. Fast-forward to last summer, when the first of the latest generation of WEP cracking tools appeared. This current generation uses a combination of statistical techniques focused on unique IVs captured and brute-force dictionary attacks to break 128 bit WEP keys in minutes instead of hours. As Special Agent Bickers noted, “It doesn’t matter if you use 128 bit WEP keys, you are vulnerable!” WEP is an encryption scheme, based on the RC-4 cipher, that is available on all 802.11a, b and g wireless products. WEP uses a set of bits called a key to scramble information in the data frames as it leaves the access point or client adapter and the scrambled message is then decrypted by the receiver. Both sides must have the same WEP key, which is usually a total of 64 or 128 bits long. A semi-random 24 bit number called an Initialization Vector (IV), is part of the key, so a 64 bit WEP key actually contains only 40 bits of “strong” encryption while a 128 bit key has 104. The IV is placed in encrypted frame’s header, and is transmitted in plain text. Traditionally, cracking WEP keys has been a slow and boring process. An attacker would have to capture hundreds of thousands or millions of packets a process that could take hours or even days, depending on the volume of traffic passing over the wireless network. After enough packets were captured, a WEP cracking program such as Aircrack would be used to find the WEP key. Fast-forward to last summer, when the first of the latest generation of WEP cracking tools appeared. This current generation uses a combination of statistical techniques focused on unique IVs captured and brute-force dictionary attacks to break 128 bit WEP keys in minutes instead of hours. Basic Directions: 1)Boot from cd 2)get the wep key 3)write it down 4)reboot into windows 5)connect using wep key. |
Password:
| Code: |
| sebs8@warezforum.info |
See Password 2.50 - Password revealing software !!!
Description:
When a password appears on screen as a series of asterisks or dots, you simply view it through SeePassword's magnifying glass to reveal the actual password text. SeePassword has no problems with passwords stored by Internet Explorer - all the sites will yield their secrets! SeePassword provides users with an easily applied retrieval tool for forgotten passwords.
Use it in many different ways. If someone has saved their password (for example, selected the "remember my password" function in Hotmail) in your computer or any public computer, then use this portable program to see there password. See what your girlfriend, partner or child is REALLY up to!!!
Download:
Code:
http://fliiby.com/file/3736/qn9935eie6.html
Subscribe to:
Comments (Atom)